Ethical Hacking:: Sniffers Videos !new!
Our mission is to improve the design process for architects and engineers. By improving the comfort of work, using a fast and intuitive interaction with the software.
GET NOW
Our mission is to improve the design process for architects and engineers. By improving the comfort of work, using a fast and intuitive interaction with the software.
GET NOW
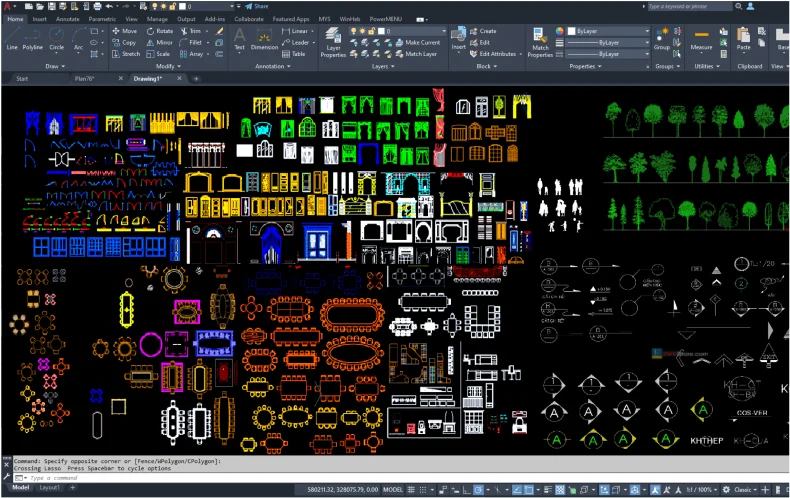
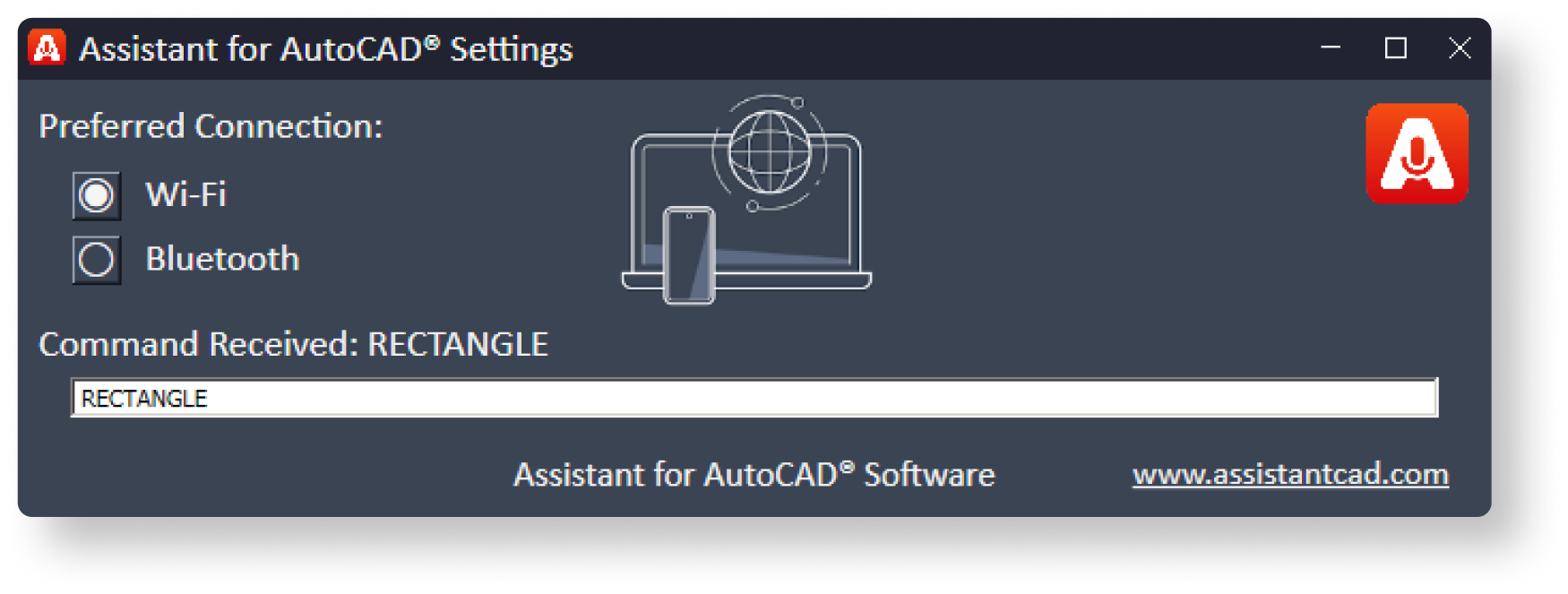
a mobile application that can execute the user's voice commands in AutoCAD










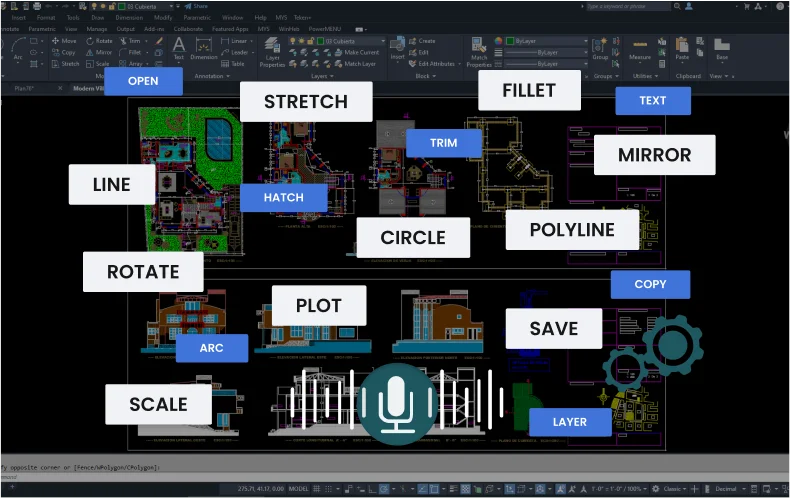
Works via Wi-Fi
runs in the background
Works via Bluetooth
Supports operation
via a headset (audio)
Basic commands
that are used most often.
Express
tool commands.
Commands
for 3d modeling.
Rarely used
AutoCAD commands

Introduction: The Double-Edged Sword of Packet Sniffing In the realm of ethical hacking, few tools are as misunderstood—or as visually compelling to demonstrate—as the network sniffer. A sniffer (or packet analyzer) is software or hardware that intercepts and logs traffic passing over a digital network. In the wrong hands, it becomes a surveillance device, capturing passwords, emails, and instant messages. In the right (ethical) hands, it is an indispensable diagnostic and security tool.
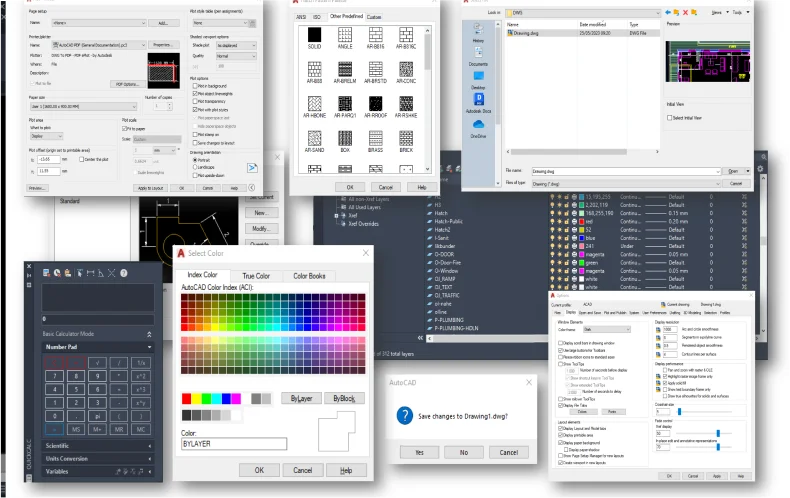
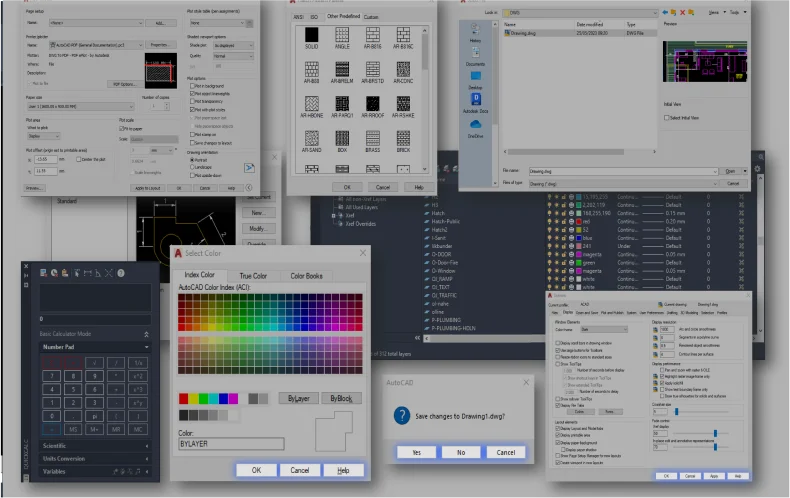
Static Blocks
Dynamic Blocks
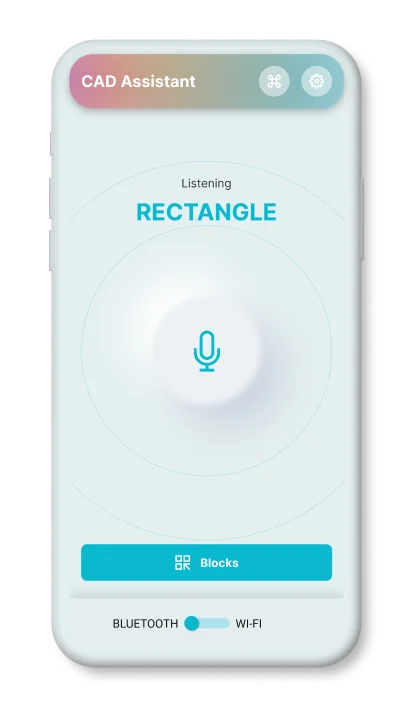
Simply speak a command to
resize or scale items.
Rapidly rotate objects or elements within the application by precisely 90 degrees. ethical hacking: sniffers videos
By issuing a voice command, you can activate the mirroring effect. Introduction: The Double-Edged Sword of Packet Sniffing In
You can effortlessly rotate blocks or objects within the application. it becomes a surveillance device
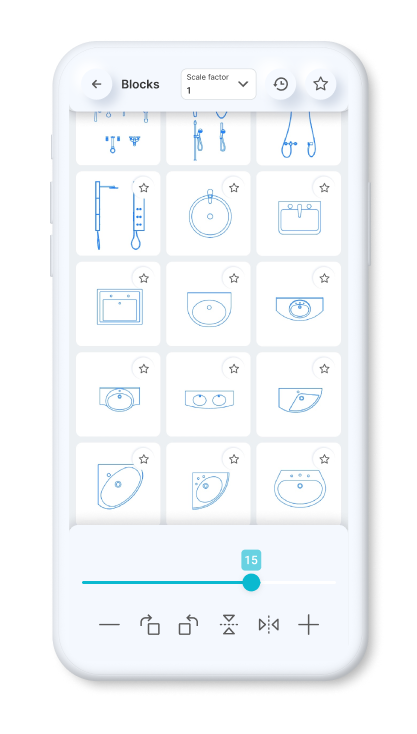
You can set a constant scale factor for your drawings to enter blocks.
Save the blocks you want most in your favorites.
Use the history page to quickly insert the last used blocks.
Standardized American
paper sizes A, B, C, D, E
Two special vertical
formats for A3 and A4

The international paper size standard is ISO 216 A4, A3, A2, A1, A0
Architectural sizes C, D, E
Introduction: The Double-Edged Sword of Packet Sniffing In the realm of ethical hacking, few tools are as misunderstood—or as visually compelling to demonstrate—as the network sniffer. A sniffer (or packet analyzer) is software or hardware that intercepts and logs traffic passing over a digital network. In the wrong hands, it becomes a surveillance device, capturing passwords, emails, and instant messages. In the right (ethical) hands, it is an indispensable diagnostic and security tool.